Remote Code Execution in Ghost CMS (CVE-2026-29053): When a Theme Becomes a Server-Side Execution Primitive
Introduction
Ghost CMS powers everything from independent blogs to large publishing platforms thanks to its flexible theming system and Node.js-based architecture. That extensibility is also where CVE-2026-29053 emerged: a vulnerability that allows specially crafted malicious themes to execute arbitrary code on the server. The issue affects Ghost CMS versions 0.7.2 through 6.19.0 and was fixed in 6.19.1.
What makes this bug especially interesting is that it is not just “a bad upload validation issue.” The deeper story is about unsafe expression evaluation, theme trust assumptions, and transitive dependency risk. A theme in Ghost is supposed to define how content looks. In the vulnerable path, however, attacker-controlled template data could flow into a JSONPath evaluator backed by static-eval, turning rendering logic into a route for JavaScript execution inside the Ghost process.

This matters because theme ecosystems are often treated as low-risk branding layers. In reality, themes can become code-bearing artifacts with privileged execution paths. In Ghost’s case, exploitation required an administrator to upload and activate a malicious theme, which means the bug sits at the intersection of application security, supply-chain trust, and admin-targeted social engineering. Once activated, the malicious logic could trigger during page rendering, making the compromise persistent and operationally dangerous.
1. Vulnerability overview
The official advisory describes the impact succinctly: a malicious Ghost theme can achieve arbitrary code execution on the server. GitHub’s advisory rates the issue High, GitLab also marks it High, and both agree on the affected version range and the fix in 6.19.1. NVD currently reflects the same vulnerable range and patch version, although its displayed scoring differs from the CNA-supplied score, which is worth noting when teams try to prioritize solely by a single CVSS number.
From a defender’s point of view, the important question is not whether exploitation is “easy,” but whether it is plausible in real workflows. In Ghost, theme installation is a legitimate administrative function. That means an attacker does not need a memory-corruption primitive or an exotic server-side deserialization chain. They need a theme package that looks acceptable enough to be installed. That shifts the threat model from anonymous internet exploitation toward malicious theme supply, insider abuse, or administrator deception.
2. Where the bug lived
The technical heart of this issue was Ghost’s get helper. In vulnerable builds, the helper’s code imported jsonpath and passed template-derived path expressions to jsonpath.query() during template processing. Endor Labs’ writeup shows the relevant behavior clearly: dynamic path resolution inside the helper was feeding attacker-influenced input into JSONPath evaluation.
That alone would already deserve scrutiny. But the real problem was further down the chain: the jsonpath package used by Ghost relied on static-eval to interpret expressions. Endor notes that Ghost had locked dependencies to jsonpath 1.1.1 and static-eval 2.0.2, and that this older static-eval line directly uses the Function() constructor for certain interpretation paths. That is exactly the kind of building block that becomes dangerous when exposed to untrusted input.
In other words, the vulnerability was not just “Ghost evaluates themes.” It was more subtle: Ghost evaluated attacker-controlled theme expressions through a dependency chain that was never a safe sandbox for hostile data. This is why the bug is such a strong case study in transitive risk. An application can look clean at the surface while still inheriting unsafe behavior from a dependency chosen for convenience years earlier.
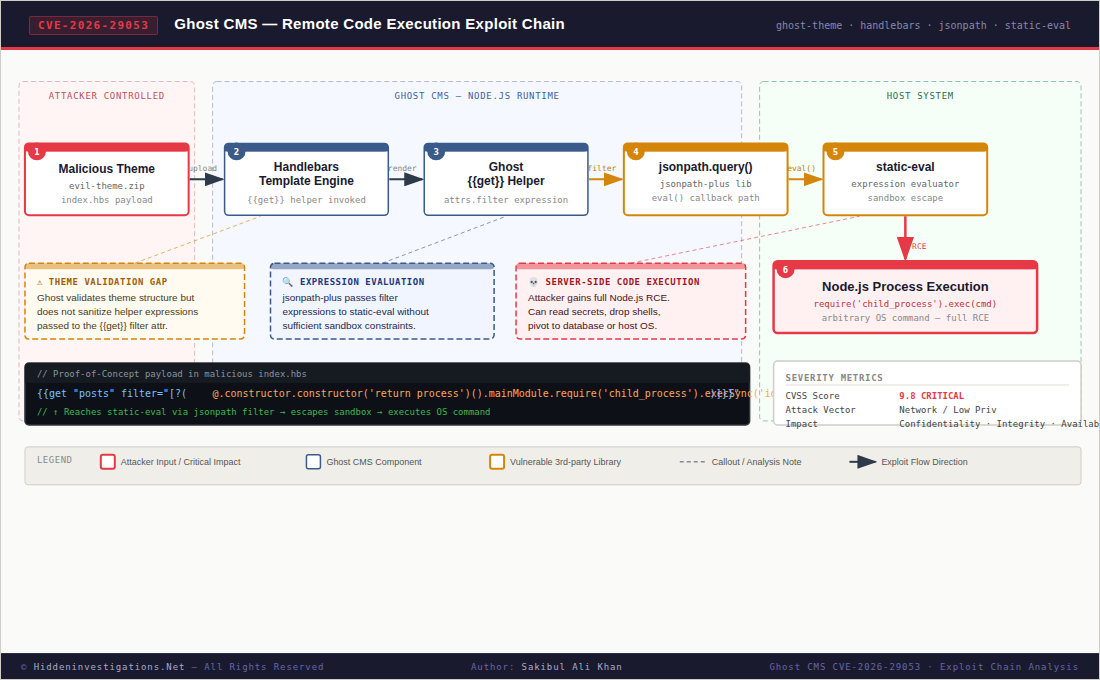
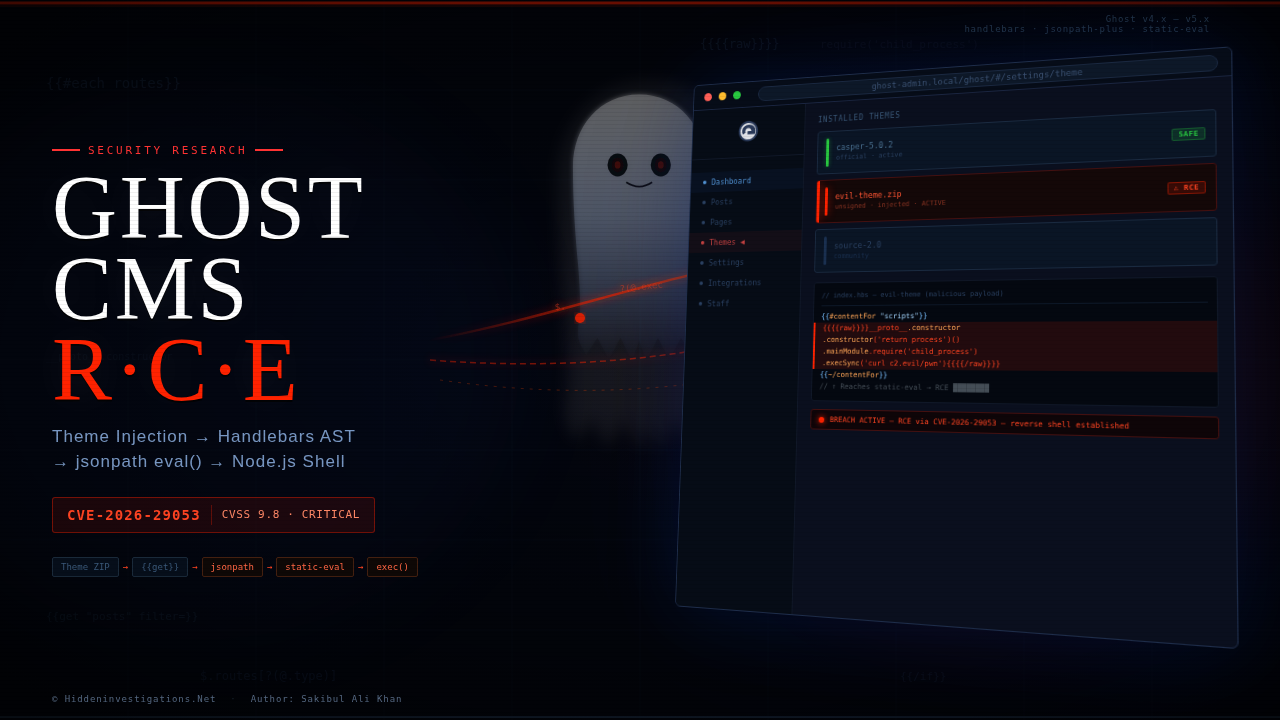
3. The exploitation path
Endor’s research showed that the vulnerable path could be reached through Ghost’s theme templates and specifically through Handlebars expressions processed by the get helper. The rendered page path mattered because the vulnerable jsonpath.query() call was reached during page generation. This is the key architectural insight: the payload did not need to live in a traditional plugin execution hook. It could live in a theme component that looked like presentation logic.
A second important piece was validation bypass. Ghost’s theme validation layer, gscan, did parse templates, but Endor found that it accepted certain single-level bracket notation patterns such as {{@site[...]}} as valid property access without deeply validating the expression inside the brackets. That gap allowed JSONPath filter-style constructs to pass validation and reach the vulnerable evaluation path.
Once there, the problem became a classic “expression sandbox escape” story. According to Endor’s analysis, the exploit did not depend on writing an obvious user-defined function directly. Instead, it used property access and JavaScript prototype behavior to reach a function object and then its constructor, ultimately recovering the ability to execute attacker-supplied JavaScript inside the Node.js runtime. That is a crucial lesson: many “safe evaluators” fail not because they allow blatantly dangerous syntax, but because the language object model itself is rich enough to reconstruct dangerous capability through indirect paths.
For safety reasons, we are not reproducing a weaponized payload here. But conceptually, the chain looked like this:
Malicious theme
-> Handlebars template with crafted get/helper expression
-> Ghost resolves dynamic path/filter
-> jsonpath.query() evaluates expression
-> static-eval interprets attacker-controlled logic
-> prototype/property access reaches executable constructor path
-> arbitrary JavaScript runs inside Ghost's Node.js processThat server-side execution context is what makes this vulnerability severe. If code runs in the Ghost process, the attacker’s options can include reading sensitive files, modifying site content, planting persistence, or moving laterally depending on how the server is deployed and what the Ghost runtime can access. Endor also notes that once the malicious theme is installed and active, the payload can be triggered on page views, which makes the compromise potentially persistent and repeatable.
4. Why this bug is more important than it first appears
CVE-2026-29053 is a strong reminder that “theme” does not mean “safe.” Modern CMS platforms often expose themes as packaging formats containing templates, helper usage, metadata, configuration, and rendering logic. Once dynamic expressions are involved, a theme stops being just a bundle of HTML and CSS and starts looking more like a low-friction extension mechanism. That has major security implications. This case shows how a feature intended for content presentation can quietly become part of the application’s code-execution surface.
It also highlights a recurring defensive blind spot: transitive dependencies used as interpreters. Many teams audit for direct uses of eval, Function, or shell execution, but far fewer scrutinize libraries that evaluate query languages, template filters, or embedded expressions. JSONPath, template engines, rule engines, markdown extensions, and AST-based “safe evaluators” all deserve the same suspicion when attacker-controlled input can reach them. Endor’s writeup is especially valuable here because it shows how the dangerous capability was not obvious at the application boundary; it emerged from the composition of Ghost, jsonpath, and static-eval.
5. Why the fix matters
One of the most instructive parts of this disclosure is the remediation story. According to Endor, a simple dependency upgrade was considered first: move to a newer jsonpath version and call it done. But that was not enough. Endor states they demonstrated that even the newer jsonpath line remained fundamentally unsafe for this use case, and they also pushed back on switching to another general-purpose evaluator because that alternative introduced denial-of-service concerns.
Ghost’s eventual decision was the right one: remove the dangerous dependency pattern rather than trying to harden it indefinitely. Endor reports that Ghost replaced the general-purpose JSONPath approach with a simpler custom path-resolution implementation tailored to the product’s real needs. The patched get.js in 6.19.1 reflects that architectural shift: the vulnerable import of jsonpath present in 6.19.0 is gone, and the code instead introduces a constrained querySimplePath routine that supports only a limited set of path semantics. That is far safer than letting a general expression engine sit in the request-to-render path.
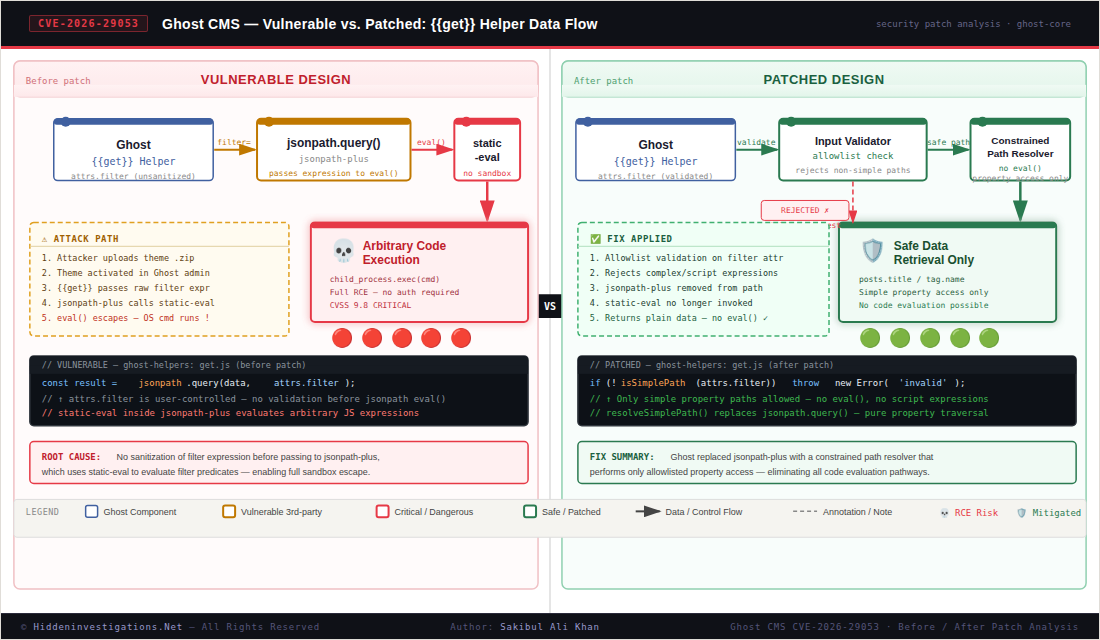
This is the deeper security lesson. When a feature only needs simple field traversal, the secure design is to build or adopt a parser that only supports simple field traversal. The moment a system imports a general evaluator for convenience, the security burden rises dramatically. Ghost’s patch is a good example of reducing capability to reduce risk.
6. Detection and incident response considerations
If you operate Ghost and suspect exposure, the first priority is versioning: anything before 6.19.1 in the affected range should be considered vulnerable and upgraded. But patching alone is not enough if an untrusted theme may already have been installed. The official advisory explicitly recommends uninstalling malicious themes and then inspecting them to understand their impact, because post-exploitation behavior can vary by payload.
From an investigative perspective, responders should review:
- theme upload and activation history in Ghost admin workflows
- recently added or modified theme packages
- suspicious Handlebars constructs around
{{#get ...}}usage - unusual bracket-notation expressions in templates
- unexpected file writes, spawned processes, or outbound connections from the Ghost Node.js process
- persistence artifacts or unauthorized content/configuration changes after a theme activation event
Those checks are a logical extension of the documented exploit path and the kind of server-side access the vulnerability can grant. Endor’s analysis makes clear that the theme becomes the delivery mechanism, while page rendering becomes the trigger.
Operationally, teams should also narrow who can upload themes, treat theme packages as code artifacts subject to review, and avoid normalizing “theme install” as a harmless branding operation. In environments where Ghost is self-hosted, runtime isolation, filesystem hardening, and least-privilege deployment can help reduce blast radius if application-level code execution is achieved.
Conclusion
CVE-2026-29053 demonstrates how expressive evaluation mechanisms embedded in customization features can introduce unexpected remote code execution paths. In Ghost CMS, the interaction between the theme system, JSONPath evaluation, and a “safe” expression engine created a boundary where untrusted input ultimately reached server-side code execution.
This case highlights a recurring class of vulnerabilities where convenience features expose interpreter-like behavior to attacker-controlled data. Mitigations are most effective when they reduce the available expressive surface rather than attempting to constrain general-purpose evaluators through layered validation. Ghost’s remediation reflects this approach by replacing a flexible evaluation mechanism with a narrowly scoped resolver.
More broadly, this vulnerability reinforces the need for careful scrutiny of parser libraries, template engines, and embedded evaluators that operate within content-processing pipelines.
References
- Endor Labs — best source for the technical root cause and fix discussion.
- GitHub Advisory — good primary advisory for affected versions, severity, and remediation.
- NVD — useful for CVE tracking, CWE mapping, and standard vulnerability reference.
- GitLab Advisory Database — useful additional advisory source for affected and fixed versions.
- SentinelOne Vulnerability Database — optional supporting reference for impact summary and defender-facing context.